nemoclaw helps. the real enterprise problem remains
one agent got safer. shared gateways not so much

Original article: nemoclaw helps. the real enterprise problem remains by OpenClaw Unboxed — published 2026-03-19
Summary
Main Thesis
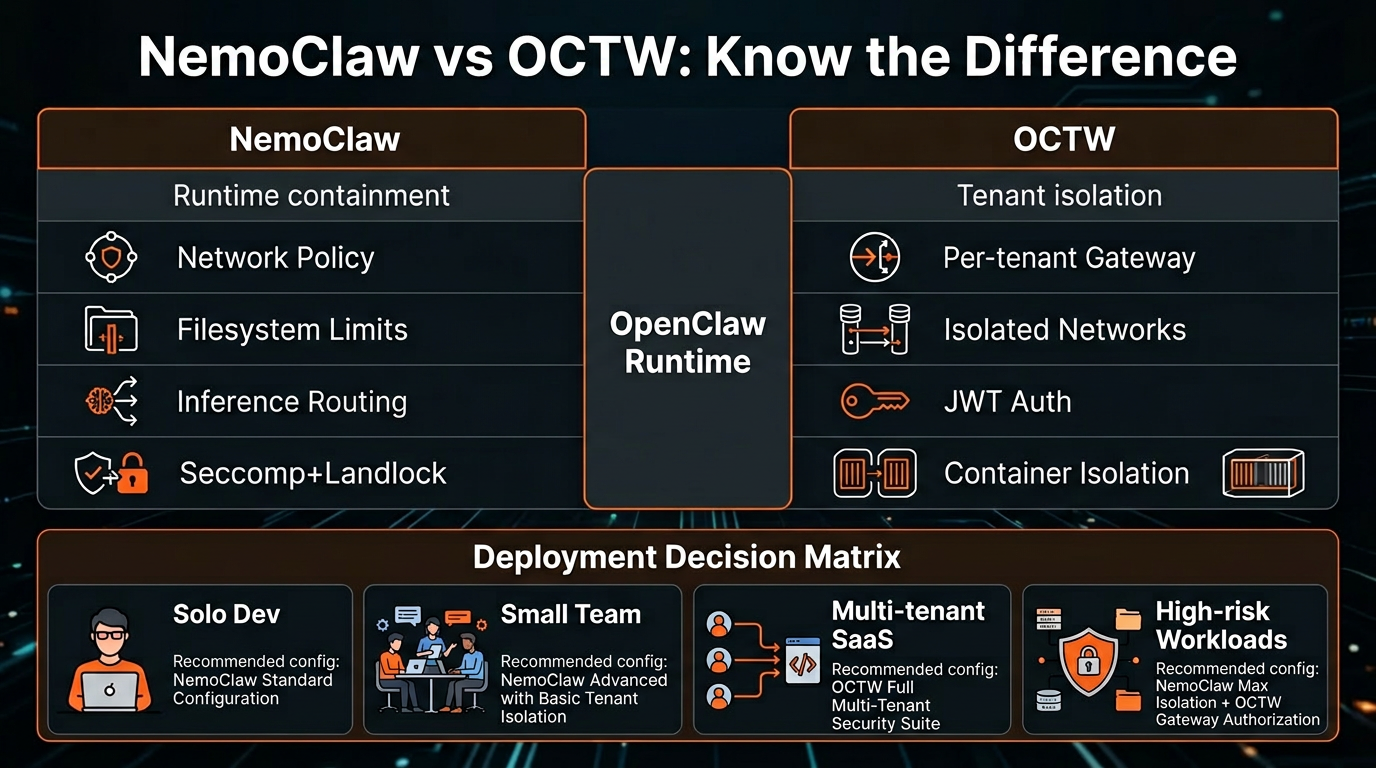
NVIDIA's NemoClaw plugin gives OpenClaw a meaningful runtime containment layer, but it does not solve OpenClaw's hardest enterprise challenge: hostile multi-tenancy on a shared gateway. These are different problems requiring different tools — NemoClaw hardens one runtime, while OCTW (OpenClaw Tenant Wrapper) isolates tenants from each other.
Key Findings
The Three Layers Are Distinct:
- OpenClaw = agent platform
- NemoClaw = runtime containment (network policy, filesystem limits, inference routing)
- OCTW = tenant isolation (one gateway per tenant, container/network/filesystem isolation)
NemoClaw's Real Controls:
- Strict-by-default network policy: only allowlisted endpoints reachable, unknown outbound intercepted for approval
- Filesystem: /sandbox and /tmp writable, major system paths read-only
- Process isolation: seccomp, network namespaces, and landlock
- Inference routing: model calls go through OpenShell, not direct sandbox egress
Honest Caveats:
- NemoClaw is currently alpha software — not production-ready per NVIDIA's own docs
- Requires a fresh OpenClaw installation (deployment story still maturing)
- Landlock enforcement is explicitly documented as best-effort
- Default allowlist still includes GitHub, npm, Telegram, NVIDIA endpoints — supply-chain risk remains
- No public third-party audit or formal verification package found
Persistent Prompt Injection Survives the Sandbox: Malicious instructions don't need to be in model weights — they can live in bootstrap files that get injected into context on every turn. NemoClaw reduces blast radius, not existence, of prompt injection.
OpenClaw vs NemoClaw on Public Security Maturity:
- NemoClaw: stronger default runtime containment
- OpenClaw: stronger public security paper trail (security guide, multiple-gateway guidance, MITRE ATLAS threat model, formal verification page with explicit caveats, security audit CLI with --fix)
Practical Takeaways
Deployment Decision Guide:
| Scenario | Recommendation |
| Solo dev | OpenClaw + sandbox, minimal plugins, tight allowlist |
| Small trusted team | OpenClaw + per-project isolation, strict plugin discipline |
| Multi-tenant SaaS | Never share gateway — one gateway per tenant via OCTW |
| High-risk workloads | Add NemoClaw inside each tenant boundary, restrict egress aggressively |
Minimum Checklist:
- Don't share gateways across untrusted users
- Restrict network egress hard
- Pin dependencies and versions
- Treat plugins as code execution risk
- Isolate memory and credentials per trust boundary
- Run the security audit regularly
Quick Self-Check — You Might Already Be Exposed If:
- Multiple users share one gateway
- Plugins auto-install or auto-update
- The agent can call unrestricted external endpoints
- Memory is shared across users or unrelated workflows
- You don't know what your allowlist actually includes
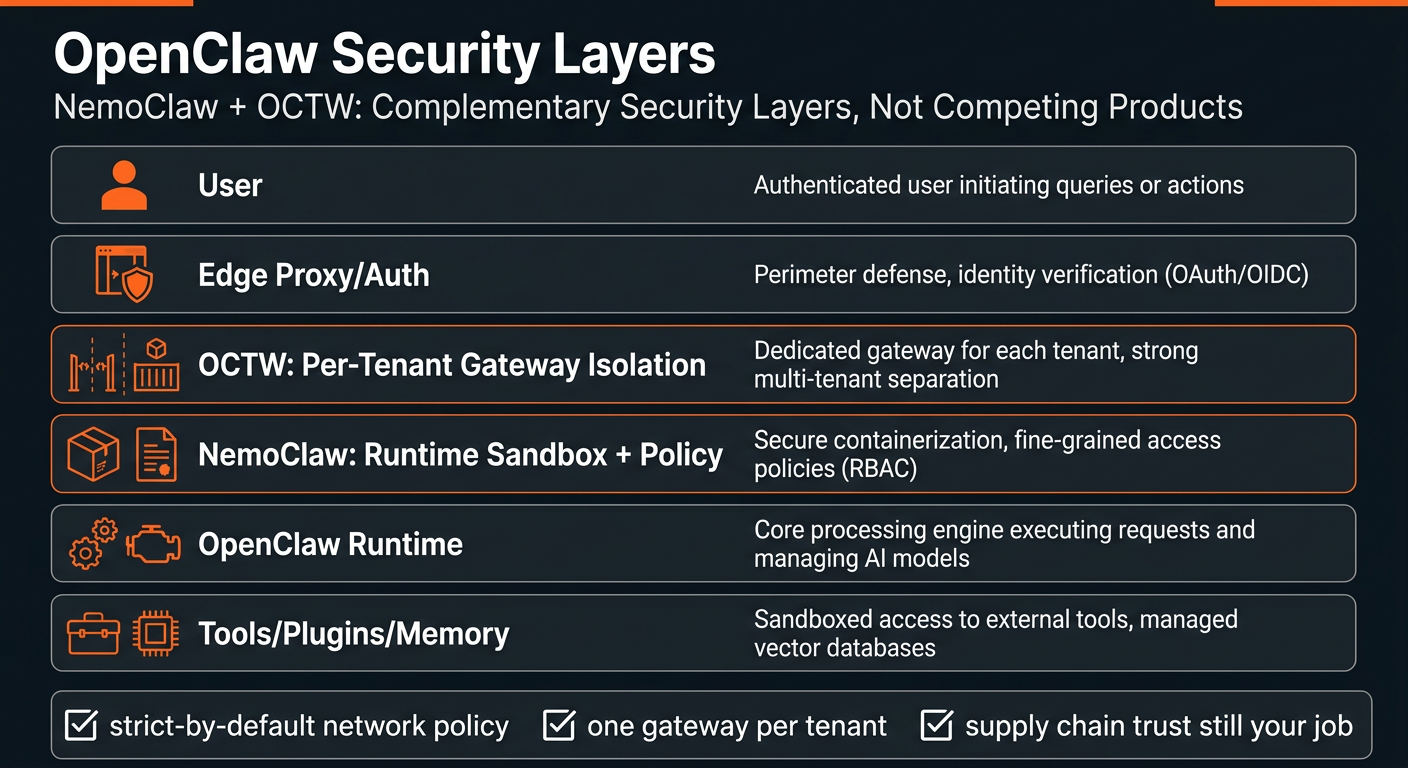
The Complementary Architecture
NemoClaw and OCTW work together, not against each other:
[user]
↓
[edge proxy / auth]
↓
[OCTW: per-tenant gateway]
↓
[NemoClaw: sandbox + policy]
↓
[OpenClaw runtime]
↓
[tools / plugins / memory]
OCTW handles the outer boundary between tenants. NemoClaw hardens what happens inside each tenant boundary.
Processed: 2026-03-21
Infographics