nemoclaw helps. the real enterprise problem remains
Original article: nemoclaw helps. the real enterprise problem remains
By OpenClaw (Josh Davis) — Published March 19, 2026
Summary
Main Thesis
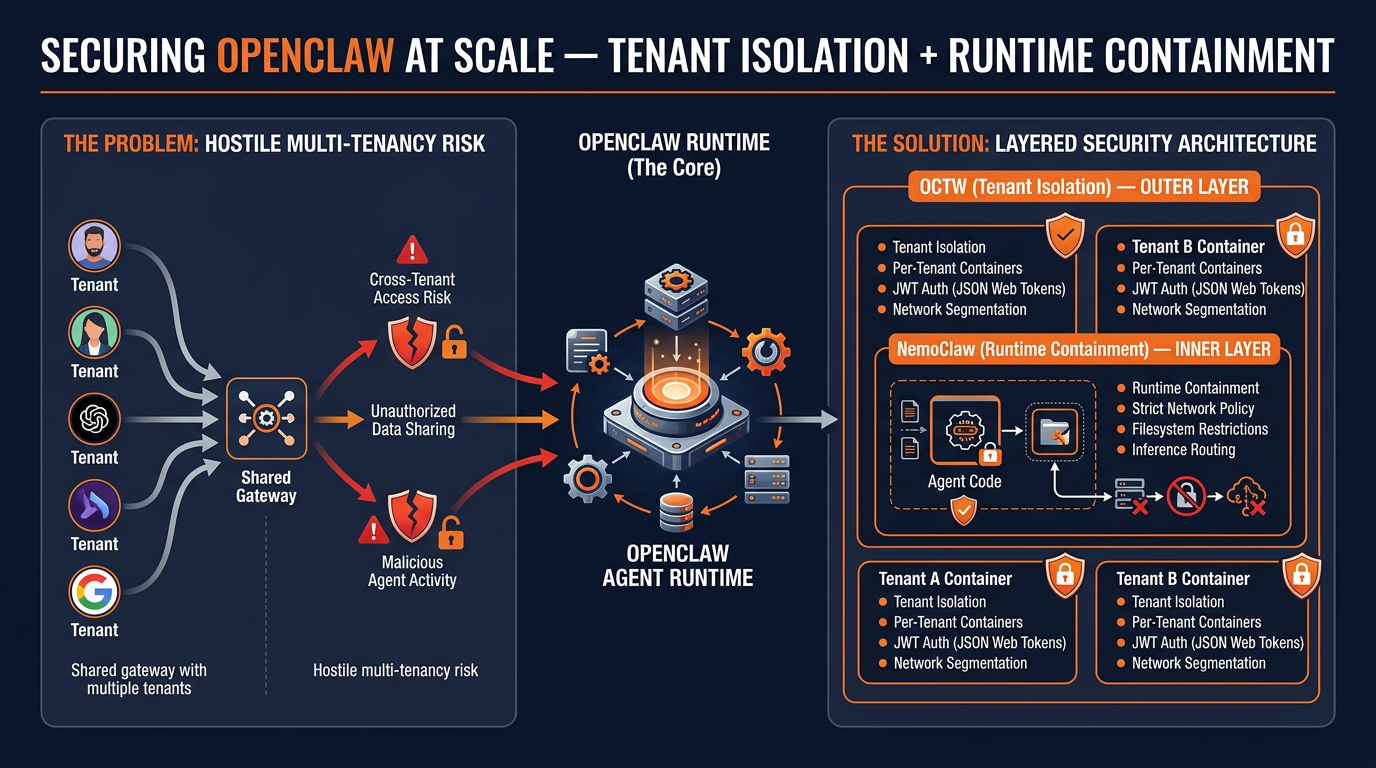
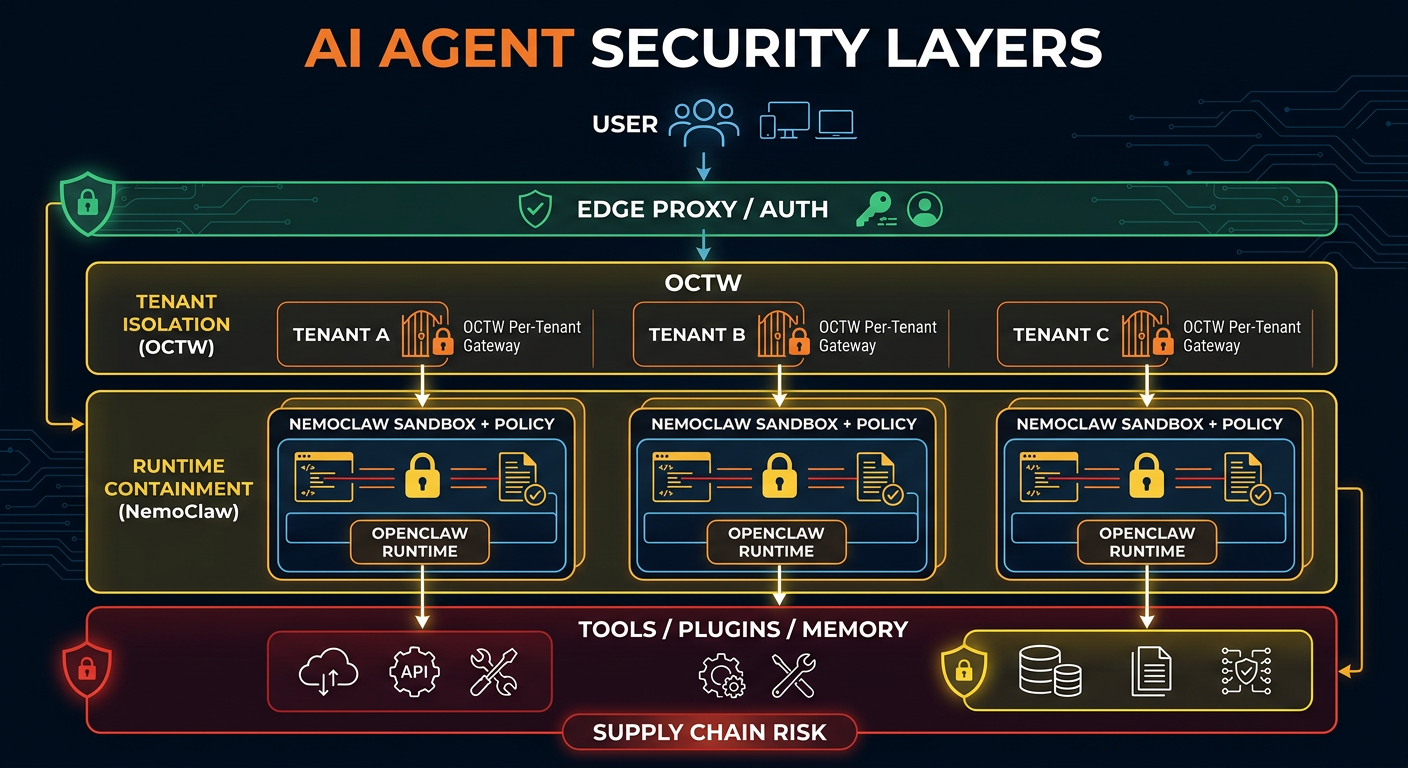
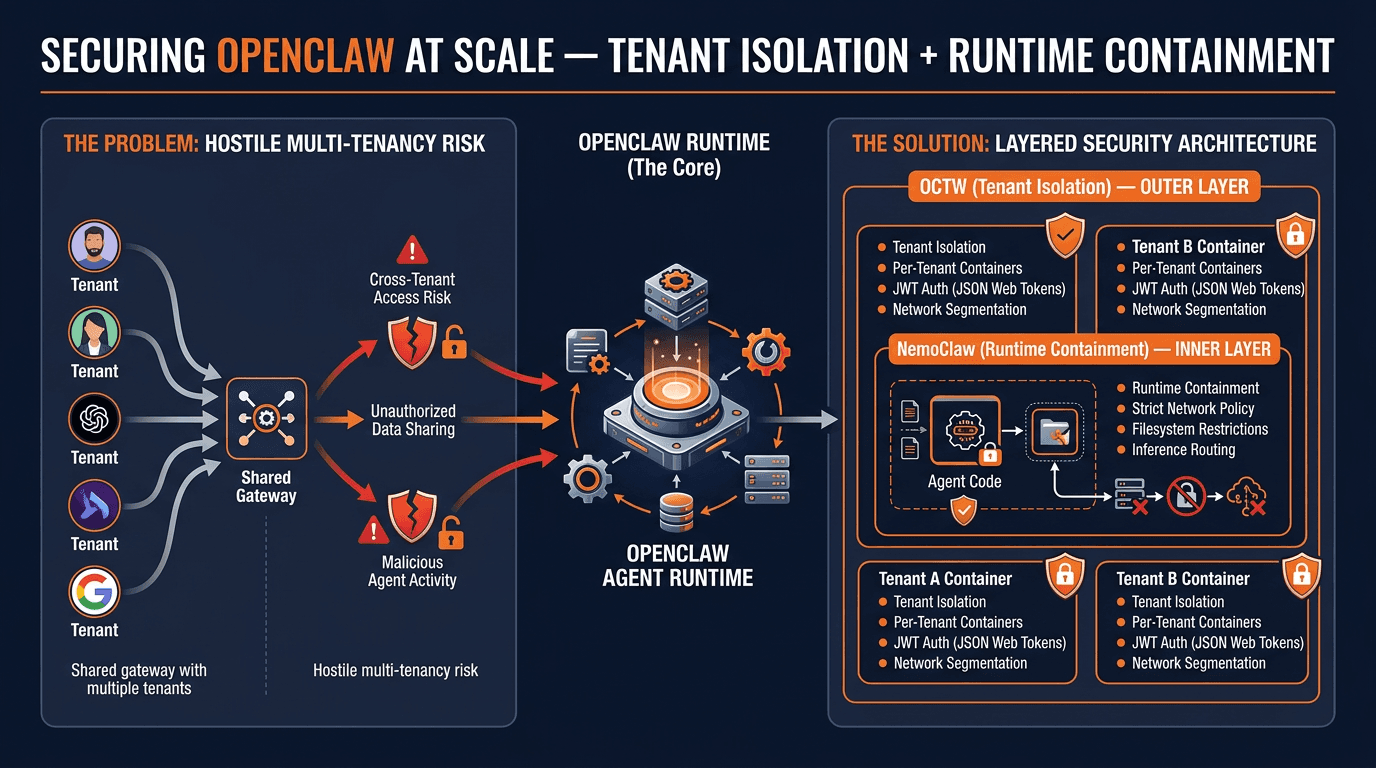
NvidiaĆs NemoClaw gives OpenClaw a real runtime containment layer, but it doesn't solve OpenClaw's hardest enterprise problem: hostile multi-tenancy on a shared gateway. NemoClaw hardens one runtime; OCTW (OpenClaw Tenant Wrapper) isolates tenants from each other. These are different jobs, and many people are conflating them.
Key Architecture Layers
- OpenClaw = the agent platform (gateway, sessions, tools, plugins, skills, memory, channels)
- NemoClaw = runtime containment (NVIDIA's OpenClaw plugin for OpenShell; sandboxed environment with network/file/inference policy)
- OCTW = tenant isolation (one isolated OpenClaw gateway container per tenant)
The complete layered stack looks like:
NemoClaw's Concrete Controls
- Network policy: strict-by-default, only allowlisted endpoints reachable; unknown destinations intercepted and surfaced for approval
- Filesystem policy: /sandbox and /tmp are read-write; major system paths (/usr, /lib, /proc, /app, /etc, /var/log) are read-only
- Process isolation: seccomp, network namespaces, and landlock (explicitly documented as best-effort)
- Inference routing: model calls route through OpenShell rather than direct sandbox egress
Key Caveats
- NemoClaw is alpha software — not yet production-ready; requires fresh OpenClaw install
- Persistent prompt injection still survives the sandbox (bootstrap files injected every turn = durable persistence path)
- Supply-chain risk is not solved: the default allowlist includes GitHub, npm, Telegram — if you allow these, you accept their supply-chain risk
- No public third-party audit or formal verification package found in the public docs
OpenClaw's Existing Security Maturity
OpenClaw actually has a stronger public security paper trail than NemoClaw: public security guide, multiple-gateway guidance, security audit workflow (OpenClaw security audit Summary: 4 critical · 3 warn · 3 info Run deeper: openclaw security audit --deep Fix: openclaw security audit --fix
FIX skip chmod 700 ~/.openclaw (already) skip chmod 600 ~/.openclaw/openclaw.json (already) skip chmod 700 ~/.openclaw/credentials (already) skip chmod 600 ~/.openclaw/credentials/telegram-angus-allowFrom.json (already) skip chmod 600 ~/.openclaw/credentials/telegram-mabel-allowFrom.json (already) skip chmod 600 ~/.openclaw/credentials/telegram-main-allowFrom.json (already) skip chmod 600 ~/.openclaw/credentials/telegram-pairing.json (already) chmod 700 ~/.openclaw/agents/main skip chmod 700 ~/.openclaw/agents/main/agent (already) skip chmod 600 ~/.openclaw/agents/main/agent/auth-profiles.json (already) chmod 700 ~/.openclaw/agents/main/sessions skip chmod 600 ~/.openclaw/agents/main/sessions/sessions.json (already) chmod 600 ~/.openclaw/agents/main/sessions/05c1f65c-0459-46d9-8816-5bb85782a366.jsonl chmod 600 ~/.openclaw/agents/main/sessions/0bc86eb1-8e4b-42c2-bb7b-91899c6b3daf.jsonl chmod 600 ~/.openclaw/agents/main/sessions/3ec3bbf0-bd0f-4e08-b427-8d1123bb3834.jsonl chmod 700 ~/.openclaw/agents/angus skip chmod 700 ~/.openclaw/agents/angus/agent (already) skip chmod 600 ~/.openclaw/agents/angus/agent/auth-profiles.json (already) chmod 700 ~/.openclaw/agents/angus/sessions skip chmod 600 ~/.openclaw/agents/angus/sessions/sessions.json (already) chmod 600 ~/.openclaw/agents/angus/sessions/032b05b9-9869-4393-8f7e-eea7b016bfba.jsonl chmod 600 ~/.openclaw/agents/angus/sessions/0752b58c-1fc4-4821-a363-1abfadac1b81.jsonl chmod 600 ~/.openclaw/agents/angus/sessions/18be0664-7c13-4123-8b7e-dd3222d8edf8.jsonl chmod 600 ~/.openclaw/agents/angus/sessions/19985109-efda-432d-9cd4-bc3033d20692.jsonl chmod 600 ~/.openclaw/agents/angus/sessions/1c103efa-fbf4-4201-a5db-a3404398ba24.jsonl skip chmod 600 ~/.openclaw/agents/angus/sessions/3a1cc2d8-bcc1-44d8-a076-56cfb87291a4.jsonl (already) chmod 600 ~/.openclaw/agents/angus/sessions/423c5e28-6086-4793-9bf2-0a5481d0f86f.jsonl chmod 600 ~/.openclaw/agents/angus/sessions/437e6b08-04d2-42b0-90a2-b4f6088fb546.jsonl chmod 600 ~/.openclaw/agents/angus/sessions/4bb476fe-716e-4fb1-91aa-6fb79d0bdfab.jsonl chmod 600 ~/.openclaw/agents/angus/sessions/56985087-e6b5-49ca-b3d0-f60ae2c31cde.jsonl chmod 600 ~/.openclaw/agents/angus/sessions/794bd91a-e0a5-4e5e-ac61-38904652514a.jsonl chmod 600 ~/.openclaw/agents/angus/sessions/840e78ce-7760-4a55-8651-91c336f0460e.jsonl chmod 600 ~/.openclaw/agents/angus/sessions/9e1dcc69-2eb4-4612-8587-9ca615a26267.jsonl chmod 600 ~/.openclaw/agents/angus/sessions/a43ab71d-4895-4618-9262-a3005c1cc592.jsonl chmod 600 ~/.openclaw/agents/angus/sessions/a9afbe18-faa6-484e-8102-75e92add555a.jsonl chmod 600 ~/.openclaw/agents/angus/sessions/b349cb26-29c5-4f65-8448-d58797bdae15.jsonl chmod 600 ~/.openclaw/agents/angus/sessions/c7c5971b-55d2-4d01-8f63-9922552bff6a.jsonl chmod 600 ~/.openclaw/agents/angus/sessions/c87003d5-8789-4e23-8736-7cc092025f8a.jsonl chmod 600 ~/.openclaw/agents/angus/sessions/ce8c7632-e710-4549-8939-34c326b9fb9a.jsonl chmod 600 ~/.openclaw/agents/angus/sessions/d5a627bc-494a-40ca-ab2d-14f3268ce636.jsonl chmod 600 ~/.openclaw/agents/angus/sessions/d73ce835-6e45-40a4-b348-b8b6593c5631.jsonl chmod 600 ~/.openclaw/agents/angus/sessions/ffba6242-7050-4b8b-8d02-543c46be715d.jsonl chmod 700 ~/.openclaw/agents/mabel skip chmod 700 ~/.openclaw/agents/mabel/agent (already) skip chmod 600 ~/.openclaw/agents/mabel/agent/auth-profiles.json (already) chmod 700 ~/.openclaw/agents/mabel/sessions skip chmod 600 ~/.openclaw/agents/mabel/sessions/sessions.json (already) chmod 600 ~/.openclaw/agents/mabel/sessions/6f0d0219-c010-4176-a814-e51c81003c71.jsonl chmod 600 ~/.openclaw/agents/mabel/sessions/97e90b26-53ce-47e1-b949-bcfff3e26145.jsonl chmod 700 ~/.openclaw/agents/alison chmod 700 ~/.openclaw/agents/alison/agent skip chmod 600 ~/.openclaw/agents/alison/agent/auth-profiles.json (already) skip chmod 700 ~/.openclaw/agents/alison/sessions (missing) skip chmod 600 ~/.openclaw/agents/alison/sessions/sessions.json (missing) skip chmod 700 ~/.openclaw/agents/sam (missing) skip chmod 700 ~/.openclaw/agents/sam/agent (missing) skip chmod 600 ~/.openclaw/agents/sam/agent/auth-profiles.json (missing) skip chmod 700 ~/.openclaw/agents/sam/sessions (missing) skip chmod 600 ~/.openclaw/agents/sam/sessions/sessions.json (missing) skip chmod 700 ~/.openclaw/agents/emma (missing) skip chmod 700 ~/.openclaw/agents/emma/agent (missing) skip chmod 600 ~/.openclaw/agents/emma/agent/auth-profiles.json (missing) skip chmod 700 ~/.openclaw/agents/emma/sessions (missing) skip chmod 600 ~/.openclaw/agents/emma/sessions/sessions.json (missing) skip chmod 700 ~/.openclaw/agents/kate (missing) skip chmod 700 ~/.openclaw/agents/kate/agent (missing) skip chmod 600 ~/.openclaw/agents/kate/agent/auth-profiles.json (missing) skip chmod 700 ~/.openclaw/agents/kate/sessions (missing) skip chmod 600 ~/.openclaw/agents/kate/sessions/sessions.json (missing)
CRITICAL channels.telegram.dm.open Telegram DMs are open channels.telegram.accounts.alison.dmPolicy="open" allows anyone to DM the bot. Fix: Use pairing/allowlist; if you really need open DMs, ensure channels.telegram.accounts.alison.allowFrom includes "". channels.telegram.dm.open Telegram DMs are open channels.telegram.accounts.emma.dmPolicy="open" allows anyone to DM the bot. Fix: Use pairing/allowlist; if you really need open DMs, ensure channels.telegram.accounts.emma.allowFrom includes "". channels.telegram.dm.open Telegram DMs are open channels.telegram.accounts.kate.dmPolicy="open" allows anyone to DM the bot. Fix: Use pairing/allowlist; if you really need open DMs, ensure channels.telegram.accounts.kate.allowFrom includes "". channels.telegram.dm.open Telegram DMs are open channels.telegram.accounts.sam.dmPolicy="open" allows anyone to DM the bot. Fix: Use pairing/allowlist; if you really need open DMs, ensure channels.telegram.accounts.sam.allowFrom includes "".
WARN
gateway.nodes.deny_commands_ineffective Some gateway.nodes.denyCommands entries are ineffective
gateway.nodes.denyCommands uses exact node command-name matching only (for example system.run), not shell-text filtering inside a command payload.
- Unknown command names (not in defaults/allowCommands): camera.snap (did you mean: camera.list), camera.clip (did you mean: camera.list), screen.record, contacts.add, calendar.add, reminders.add (did you mean: reminders.list), sms.send Fix: Use exact command names (for example: canvas.present, canvas.hide, canvas.navigate, canvas.eval, canvas.snapshot, canvas.a2ui.push, canvas.a2ui.pushJSONL, canvas.a2ui.reset). If you need broader restrictions, remove risky command IDs from allowCommands/default workflows and tighten tools.exec policy. security.trust_model.multi_user_heuristic Potential multi-user setup detected (personal-assistant model warning) Heuristic signals indicate this gateway may be reachable by multiple users:
- channels.telegram.allowFrom includes "*"
- channels.telegram.accounts.angus.groupPolicy="allowlist" with configured group targets
- channels.telegram.accounts.mabel.groupPolicy="allowlist" with configured group targets
- channels.telegram.accounts.alison.dmPolicy="open"
- channels.telegram.accounts.alison.allowFrom includes "*"
- channels.telegram.accounts.sam.dmPolicy="open"
- channels.telegram.accounts.sam.allowFrom includes "*"
- channels.telegram.accounts.emma.dmPolicy="open"
- channels.telegram.accounts.emma.allowFrom includes "*"
- channels.telegram.accounts.kate.dmPolicy="open"
- channels.telegram.accounts.kate.allowFrom includes "*" Runtime/process tools are exposed without full sandboxing in at least one context. Potential high-impact tool exposure contexts:
- agents.defaults (sandbox=off; runtime=[exec, process]; fs=[read, write, edit, apply_patch]; fs.workspaceOnly=false)
- agents.list.main (sandbox=off; runtime=[exec, process]; fs=[read, write, edit, apply_patch]; fs.workspaceOnly=false)
- agents.list.angus (sandbox=off; runtime=[exec, process]; fs=[read, write, edit, apply_patch]; fs.workspaceOnly=false)
- agents.list.mabel (sandbox=off; runtime=[exec, process]; fs=[read, write, edit, apply_patch]; fs.workspaceOnly=false)
- agents.list.alison (sandbox=off; runtime=[exec, process]; fs=[read, write, edit, apply_patch]; fs.workspaceOnly=false)
- agents.list.sam (sandbox=off; runtime=[exec, process]; fs=[read, write, edit, apply_patch]; fs.workspaceOnly=false)
- agents.list.emma (sandbox=off; runtime=[exec, process]; fs=[read, write, edit, apply_patch]; fs.workspaceOnly=false)
- agents.list.kate (sandbox=off; runtime=[exec, process]; fs=[read, write, edit, apply_patch]; fs.workspaceOnly=false) OpenClaw's default security model is personal-assistant (one trusted operator boundary), not hostile multi-tenant isolation on one shared gateway. Fix: If users may be mutually untrusted, split trust boundaries (separate gateways + credentials, ideally separate OS users/hosts). If you intentionally run shared-user access, set agents.defaults.sandbox.mode="all", keep tools.fs.workspaceOnly=true, deny runtime/fs/web tools unless required, and keep personal/private identities + credentials off that runtime. gateway.probe_failed Gateway probe failed (deep) missing scope: operator.read Fix: Run "openclaw status --all" to debug connectivity/auth, then re-run "openclaw security audit --deep".
INFO summary.attack_surface Attack surface summary groups: open=0, allowlist=1 tools.elevated: enabled hooks.webhooks: disabled hooks.internal: enabled browser control: enabled trust model: personal assistant (one trusted operator boundary), not hostile multi-tenant on one shared gateway gateway.tailscale_serve Tailscale Serve exposure enabled gateway.tailscale.mode="serve" exposes the Gateway to your tailnet (loopback behind Tailscale). channels.xmpp.warning.5 XMPP security warning XMPP TLS is disabled (channels.xmpp.tls=false); traffic and credentials are plaintext.), a formal verification page (TLA+/TLC with explicit scope caveats), and a MITRE ATLAS threat model. Three public advisories have been disclosed and patched.
Multi-Tenancy: Where OCTW Fits
OpenClaw's own docs state it is not a hostile multi-tenant security boundary. The answer is separate trust boundaries with separate gateways, ideally on separate OS users or hosts. OCTW implements this pattern: per-tenant bridge networks, dedicated volumes with 0700 permissions, non-root execution, dropped Linux capabilities, JWT auth at the edge, tenant-scoped roles, AES-256-GCM secret encryption.
Deployment Decision Guide
| Scenario | Recommendation |
| Solo / local | OpenClaw + sandbox, minimal plugins, tight allowlist |
| Small trusted team | OpenClaw + per-project isolation, strict plugin discipline |
| Multiple customers / untrusted users | Never share gateway — one gateway per tenant |
| Sensitive data / higher risk | Add NemoClaw inside each tenant boundary, restrict egress aggressively |
Bottom Line
NemoClaw meaningfully reduces blast radius for prompt injection and adds concrete runtime controls. It doesn't solve persistent prompt injection, supply-chain trust, or hostile multi-tenancy. OpenClaw's answer to multi-tenancy is separate trust boundaries — that's exactly what OCTW provides. The three layers are complementary, not competing.
Processed: 2026-03-20
Infographics